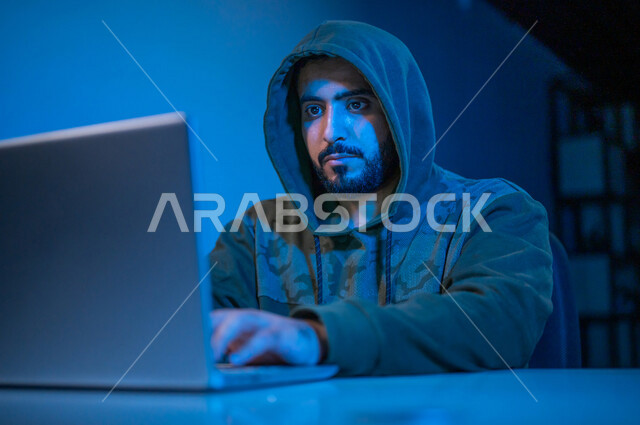
A Saudi Arabian Gulf youth, working in the field of illegal hacking, hacking the protection, security and privacy of users, using the computer for illegal purposes, electronic crimes

Important information
Signed model release License agreement





















We use cookies to provide for you a better experience. For more information check our Cookie policy.