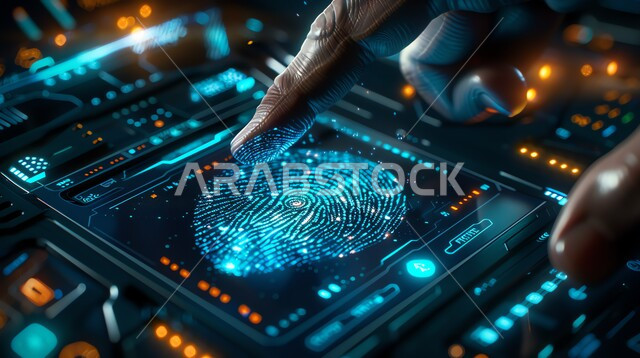
Securing and protecting sensitive information from cyber attacks using fingerprint scanning concept, cyber security and information preservation concept, close-up of a Saudi Arabian Gulf man's hand pressing his finger to unlock a security lock using modern technology, fingerprint scanner, fingerprint entry security system